Risk Register: Complete Guide to Creating and Managing an Effective Risk Register in 2026
The risk register, also known as a risk log or risk management register, is one of the most essential tools in modern risk management and project risk management. It is a structured document used to identify, analyze, prioritize, and monitor risks that could affect a project, organization, or operational strategy. Companies increasingly rely on risk registers to centralize risk information and maintain visibility over potential threats that could disrupt timelines, budgets, or strategic objectives. In 2026, organizations operate in a business environment characterized by rapid digital transformation, complex supply chains, cybersecurity threats, and regulatory pressure. According to recent global risk management reports published in 2026, over 72% of enterprise-level projects now maintain a formal risk register to improve governance and decision-making. A well-structured register allows teams to anticipate issues early, coordinate mitigation actions, and create a proactive culture of risk awareness across departments and stakeholders.
What Is a Risk Register and Why It Matters
A risk register is a centralized document or database that records all identified risks related to a project, program, or organization. It plays a critical role in the broader risk management framework, enabling teams to document risk descriptions, probability levels, potential impacts, and mitigation strategies. Unlike a simple list of potential threats, a risk register provides detailed analytical information that supports prioritization and strategic planning. By structuring risk data in a consistent format, organizations can evaluate risks objectively and ensure that every critical threat receives appropriate attention. This structured approach transforms risk management from reactive crisis handling into a proactive process focused on anticipation, mitigation, and continuous monitoring.
Risk Register vs Risk Log vs Risk Matrix
The terms risk register, risk log, and risk matrix are often used together in risk management discussions, but each tool serves a distinct purpose within a project governance framework. A risk log typically represents a simplified list of identified risks, often used for quick tracking during meetings or project updates. A risk register expands on this list by including detailed attributes such as impact assessment, probability scoring, ownership, and mitigation plans. The risk matrix, also called a probability-impact matrix, provides a visual framework to prioritize risks based on severity and likelihood. In effective project risk management, these tools complement each other by combining structured documentation with visual prioritization to guide decision-making.
The Strategic Benefits of Using a Risk Register
Organizations implement a risk register in project management primarily to improve strategic visibility and proactive planning. By identifying potential threats early in the project lifecycle, teams can allocate resources more effectively and avoid costly disruptions. Risk registers also enhance collaboration among stakeholders by providing a shared reference point for risk discussions and mitigation strategies. This transparency ensures that all parties understand the potential threats facing the project and the actions required to address them. Additionally, a structured risk register supports compliance with governance standards such as ISO 31000, enterprise risk management frameworks, and regulatory requirements.
Improving Strategic Decision-Making
A well-maintained risk management register provides decision-makers with reliable data to evaluate uncertainties and prioritize actions. Each recorded risk includes measurable attributes such as probability, impact level, and response strategy, enabling leaders to compare risks objectively. This structured analysis reduces reliance on intuition and encourages data-driven decision-making. Executive teams often use aggregated risk register data to inform strategic planning sessions and investment decisions. By integrating risk insights into governance dashboards and reporting frameworks, organizations can align operational decisions with long-term strategic objectives.
Strengthening Stakeholder Communication
The project risk register also plays an important role in communication across teams and departments. Complex projects often involve multiple stakeholders, including managers, engineers, suppliers, and executive sponsors, each with different perspectives on potential threats. A centralized register ensures that everyone works from the same information and understands the status of each identified risk. Clear ownership assignments and documented mitigation actions improve accountability and coordination. As a result, organizations can respond faster to emerging issues and maintain stronger alignment between operational teams and leadership.
Key Components of an Effective Risk Register
A strong risk register template includes structured fields that allow teams to document and analyze risks consistently across projects and departments. Standardizing these elements ensures that risk assessments remain comparable and measurable over time. Organizations often customize their risk register structure depending on industry, regulatory requirements, and project complexity. However, certain core elements appear in almost every effective register because they provide the essential information required for prioritization and response planning. These components allow project teams and executives to quickly understand the nature of each risk and determine appropriate actions.
Essential Fields in a Risk Register
An effective risk register example typically includes multiple structured data points that allow organizations to analyze and monitor risks systematically. These fields transform a simple risk list into a powerful analytical tool capable of supporting strategic decisions and operational responses. Many organizations standardize these attributes across all projects to ensure consistency in reporting and governance. The following elements represent the most common fields used in professional risk registers.
- Risk ID to uniquely identify and track each risk
- Risk description explaining the potential threat and its cause
- Probability rating estimating the likelihood of occurrence
- Impact assessment evaluating financial, operational, or reputational consequences
- Risk score or priority calculated from probability and impact values
- Risk owner responsible for monitoring and mitigation
- Mitigation or response strategy outlining actions to reduce the risk
- Status and review date ensuring continuous monitoring
Advanced organizations often expand this structure to include additional attributes such as risk triggers, detection indicators, residual risk levels, and mitigation costs. These additional data points provide deeper insights into risk dynamics and help organizations anticipate future developments. When integrated into project management tools or enterprise governance systems, these structured fields enable automated reporting and trend analysis across multiple projects.
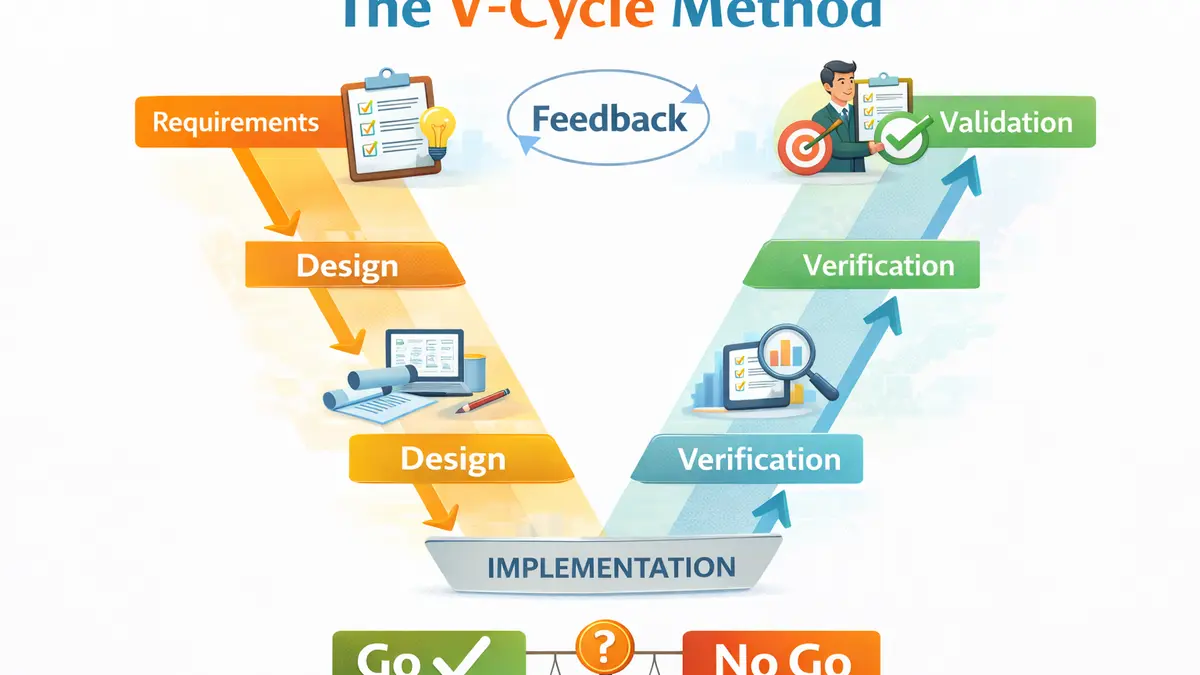
How to Create a Risk Register Step by Step
Building a risk register for project management requires a structured process that combines risk identification, analysis, response planning, and continuous monitoring. International frameworks such as ISO 31000 and the Project Management Institute (PMI) guidelines provide widely accepted methodologies for implementing this process. The goal is to ensure that risk management becomes an ongoing discipline rather than a one-time planning activity. By integrating the risk register into regular governance meetings and project workflows, organizations can maintain visibility over potential threats throughout the entire lifecycle of a project.
Step 1: Identify Potential Risks
The first stage of building a risk register involves identifying all potential threats that could affect the success of a project or operation. Teams typically conduct workshops, brainstorming sessions, and historical data analysis to uncover risks across technical, financial, operational, and regulatory dimensions. Consulting past project documentation and industry benchmarks can reveal common patterns of risk that may otherwise be overlooked. The objective is to develop a comprehensive inventory of possible threats before evaluating their likelihood or severity. A thorough identification phase significantly increases the effectiveness of subsequent risk analysis and mitigation planning.
Step 2: Evaluate Probability and Impact
Once risks have been identified, teams must assess their probability of occurrence and potential impact on project objectives. This evaluation often relies on a risk register matrix, which categorizes risks based on severity and likelihood. Organizations may use qualitative scales such as low, medium, and high, or quantitative scoring systems to measure risk levels. The result is a prioritized list of threats that require monitoring or immediate action. By ranking risks according to their potential consequences, teams can focus resources on the issues most likely to disrupt project outcomes.
Step 3: Define Risk Response Strategies
After analyzing risk severity, teams must determine appropriate response strategies for each identified threat. Standard risk response approaches include avoidance, mitigation, transfer, and acceptance, depending on the risk level and organizational tolerance. Mitigation plans typically involve specific actions designed to reduce the probability or impact of a risk. In some cases, organizations also develop contingency plans that can be activated if a risk materializes. Documenting these strategies in the risk register ensures that teams can respond quickly and consistently when risk indicators appear.
Risk Register Example in a Real Project
A practical project risk register example illustrates how risk data is documented and monitored within a real business environment. Consider a large digital transformation initiative involving cloud migration and system modernization. Potential risks may include service downtime during migration, budget overruns caused by infrastructure complexity, or resistance from employees adapting to new workflows. Each risk entry would contain probability and impact assessments, mitigation strategies, and assigned owners responsible for monitoring progress. This structured documentation enables project leaders to track risk exposure in real time and adjust strategies as new information emerges. Over the course of the project lifecycle, the register evolves to reflect changing conditions and newly identified threats.
Best Practices for Maintaining a High-Quality Risk Register
The value of a risk register template depends not only on its structure but also on how consistently it is maintained and integrated into governance processes. A risk register should never remain static after its initial creation because project conditions and external factors constantly evolve. Organizations that successfully manage risk treat the register as a living document that evolves alongside operational activities. Regular updates and reviews ensure that emerging threats are captured and mitigation strategies remain relevant. By embedding risk management into daily workflows, teams strengthen their ability to anticipate and respond to challenges before they escalate.
Conduct Regular Risk Reviews
Periodic risk review meetings play a crucial role in maintaining the effectiveness of the risk register. During these sessions, stakeholders evaluate the status of existing risks, assess the effectiveness of mitigation actions, and identify any newly emerging threats. Depending on the complexity of the project, these reviews may occur weekly, monthly, or at major project milestones. The insights generated from these discussions often lead to adjustments in risk scores, mitigation plans, or ownership assignments. Continuous review ensures that the risk register remains aligned with the evolving realities of the project environment.
Assign Clear Ownership for Each Risk
Every risk listed in a risk management register should have a clearly defined owner responsible for monitoring its status and implementing mitigation actions. Without clear accountability, risks may remain documented but unresolved, reducing the effectiveness of the entire risk management process. The designated risk owner tracks early warning indicators, reports progress during review meetings, and coordinates response efforts if the risk materializes. This approach ensures that each risk receives appropriate attention and that mitigation strategies are executed as planned. Establishing clear ownership also strengthens accountability across teams and promotes a culture of proactive risk management.
Risk Register FAQ
What is a risk register in project management?
A risk register in project management is a structured document used to identify, analyze, and monitor risks that could affect a project’s objectives. It records key information about each risk, including probability, potential impact, mitigation strategies, and assigned ownership. By centralizing this information, project teams gain a clear overview of potential threats and can prioritize mitigation efforts accordingly. The risk register is typically updated throughout the project lifecycle to reflect new risks and evolving circumstances.
Why is a risk register important for organizations?
A risk register provides organizations with a structured approach to identifying and managing uncertainties that could affect operational performance or strategic objectives. By documenting risks and mitigation plans in a centralized system, companies can improve transparency, accountability, and decision-making. This proactive approach reduces the likelihood of unexpected disruptions and supports compliance with governance and regulatory standards. Organizations that maintain well-structured risk registers are generally better prepared to respond to emerging threats.
How often should a risk register be updated?
The frequency of risk register updates depends on project complexity and organizational risk tolerance. In many cases, teams review the register during weekly or monthly project governance meetings to ensure that information remains accurate and relevant. High-risk environments such as cybersecurity or infrastructure projects may require more frequent monitoring and updates. Regular updates ensure that emerging threats are captured quickly and that mitigation strategies remain effective as project conditions change.